We recently welcomed a new team member to the Way We Do family. Jonah Sargeant is our customer success guru, supporting new and existing customers as they put Way We Do to work in their organizations.
The daily cadence at Way We Do is that every team member gives a daily stand up – a message via our collaboration app that lets the rest of the team know what they did yesterday, what they’ll be working on today, and whether they’ll need any help with anything.
Some of our team members meet with their line manager to run through their their daily stand up verbally. Naturally, we use Way We Do to help us manage these meetings.
The email request…
One morning, Jonah asked me about a request from Dan, one of Way We Do’s founders and directors, about purchasing something for him. I wasn’t aware Dan needed anything and I was curious.
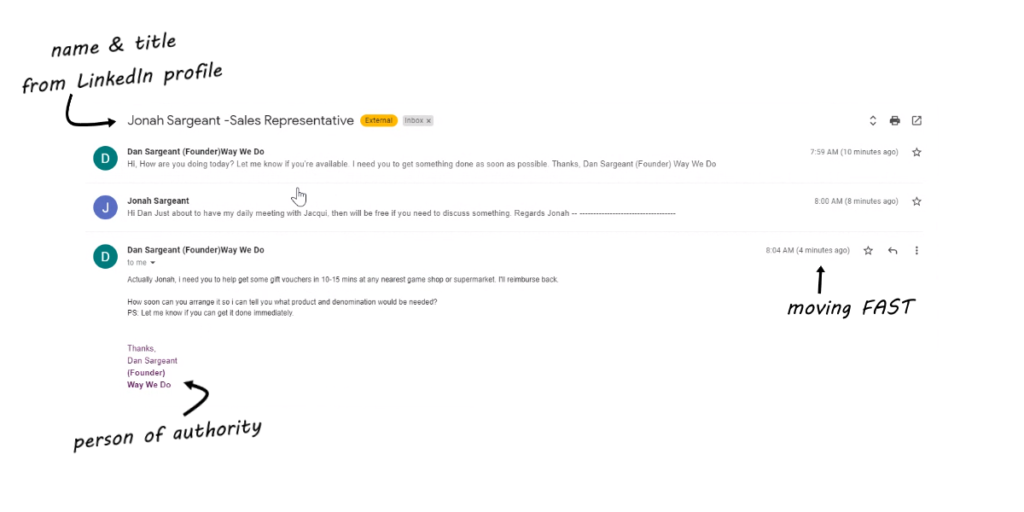
Jonah showed me “Dan’s” email. Naturally, as a new employee, Jonah sees Dan as an authority figure, and dutifully replied, saying he’d happily discuss it with him after his regular meeting with his line manager (me).
“Dan” replied, saying he needed Jonah to purchase gift vouchers in the next few minutes, and that he’d be reimbursed later. To create further urgency, the email used phrases like “next 10-15 minutes”, “how soon”, and “get it done immediately”.
Any young employee who has just started working with a company, and who may still be new to the workforce would be highly sensitive to this kind of language and would feel compelled to complete the task. After all, you wouldn’t want to let the boss down on your first week on the job. You want to make a good impression.
Needless to say, the alarm bells were ringing for me. Dan wouldn’t ask a team member to use their own money to purchase gift vouchers! It’s an unusual request and highly out of character. I immediately told Jonah it was a scam. Our information security practice is for team members to immediately alert their line manager or our CTO of any real or perceived breaches or breach attempts.
Scammers use LinkedIn to gather information
We examined the email and could see how advanced this particular scammer was. They had great use of casual English, and they were working fast. Jonah received the email 10 minutes prior and responded within two minutes. Within four minutes, the player could see the game was on and was pressing Jonah to take action.
Cleverly, the email’s subject heading contained Jonah’s full name and role title – a well-known email marketing technique to increase open rates and get the person reading the email.
Another element people look for when deciding whether to open an email is who it’s from. The supposed sender “Dan Sargeant (Founder)Way We Do” was instantly recognizable to Jonah, as he knows Dan as being one of the directors of the business and his employer. So of course he opened it as soon as he saw it.
We saw the information about Jonah and Dan had come directly from LinkedIn. Scammers are continually monitoring the social channel for anyone who has just joined a company as a new employee. They’re targeted precisely because they’re new, and may not necessarily be fully across what is usual practice within the business.
My own professional background in email marketing tells me the scammers will most certainly be either scraping data from LinkedIn, or hiring low-cost data entry labor to fill their databases. They then send out emails at scale, but individually so they make it through spam detection filters.
Is the scammer an individual acting on their own or as part of an organized crime center with a room of operators anticipating vulnerable people responding to their emails? Is the scammer from Russia or another stereotypically dodgy location? The truth is, when there is large-scale global disruption as a result of COVID, the war in Ukraine, and increasing occurrences of natural disasters, the climate is ripe for criminals anywhere to exploit the situation for their own ends. They might even be in your own neighborhood.
Protecting your LinkedIn profile
Being new to LinkedIn, Jonah created his profile without enabling any security features. But after this real-life encounter, he activated all the security features he could find. Unfortunately, that left his profile appearing simply as “LinkedIn Member”, no image, no information. Just a faceless person on the Internet.
But as a professional who’s building a career, a reputation, maybe even a business, you want your existing and prospective network to know who you are. It’s why LinkedIn exists. There has to be a balance between letting anyone access your entire network and all your details on LinkedIn, and creating a solid profile that represents who you are.
Building trust online includes creating genuine profiles and providing a digital footprint that shows you’re a real person. It’s hard to trust a person in the B2B world who has very little in terms of a digital footprint. It’s like having no credit rating. We tend not to want to do business with companies that don’t have a website, and that aren’t registered in the country they’re operating in. It’s harder to determine an individual is legitimate if they don’t have an online profile that affirms who they are and what they stand for makes it harder to know if they are legitimate.
Blog posts and videos that demonstrate thought leadership in your field can help your existing and prospective customers know you’re real and feel a stronger sense of trust in your business. These forms of outreach help you claim your voice and deliver a unique message that can make a difference in the communities you serve. It’s important that we keep the lights in our world shining, so they can continue to deliver their value through platforms like LinkedIn.
At Way We Do, we carry out due diligence on all new organizations that sign up to our platform. This bears a cost in both time and money for us, but it’s important for us to know who we’re doing business with. We’re not a firm that’s all about signing up as many people as we can as quickly as we can without returning any real substance to our customers. We’re about quality connections and solutions that will make a real impact for the companies we work with all around the world. We know we’re not alone in that aspiration. A legitimate LinkedIn profile helps us know who our customers are as much as it is about them knowing who we are. Trust is a two-way street.
Team Cyber Security Training
Cyber security is not something you can abdicate to your IT team. It’s everyone’s responsibility. As a business leader, no matter what size business you run, you must lead security and work in partnership with your IT professionals. Cyber Security is an enabler for growth, because without trust, you cannot run your business successfully. In days gone by, we knew our banker, our grocer, our mailman. As products, services, and client relationships move more and more to online delivery, good security is indispensable for building trust.
Training your team on cyber security is mission critical in today’s world, especially with increasing rates of cyber crime. Cyber Security and an Information Security Management System, is vital for every modern organization.
Back to that dodgy email
In the email Jonah received, there was a visual indicator that the email came from an external source. Technology developments like this make it easier for your team members to recognize when an email is legitimate (or not!).
But Cyber Security isn’t just about technological controls. It’s about people, organizational and physical controls. Your team are the frontline of your business and you need to train them to recognize threats. Teach them what signals to look out for, when to check out something that doesn’t look quite right, and not dismiss their instincts. Make sure they know what to do, and who to talk to when they find something. It’s “stranger danger” training for the workplace.
Final words…
So, Jonah, welcome to Way We Do (even though this experience was a little alarming during your first days on the job). We’re really pleased and proud to have you as part of our team. We’re all going to have a lot of fun together AND we’re on a mission to help our customers’ be as resilient as they can be.
To our customers, if you’d like to explore Information Security Management further with Way We Do and our Service Partners, just reach out to support@waywedo.com for further details.
Understand that cyber incidents will occur. But knowledge is power. We’re here to help you put practices in place that will reduce the risk of cyber attacks harming your business, your customers, and your team.